Hackers who target bugs also hack WordPress pages. Currently, every minute, there are about 90,000 assaults on WordPress pages.
If they are successful, they will use the website to run all sorts of fraudulent activities-steal consumer information, market illicit goods, send spam emails (read-phishing hack), dupe consumers into malware downloading, use black hat SEO methods to rate their own products (read-pharma hack), instal backdoors-the list goes on.
Being hacked is not a terrible news for a website user, it is a disaster! And on any place, large or small, it can happen. It’s fascinating to remember that smaller websites claim hackers aren’t going to come after them. But in fact, such websites are easy targets and hackers like them.
You have a lot to lose if the site gets compromised. Your clients will no longer trust your website, your profits and income will take a dive, and Google could even blacklist you, and your WordPress web host will suspend you.
If all this scares you about the security of your site, we’ve got you covered. We’ll get behind the mindset of hackers in this article and explain the aspects in which they infiltrate websites. After that we’ll even discuss means of neutralising them.
TL;DR
Hackers have at their disposal a legion of hacking tactics that can try to obtain access to your site. Using the Hack Protection Plugin for MalCare to keep hackers at bay. MalCare will protect the website proactively from malware, warn you to any interference, and assist you to prevent any sort of contamination.
You must understand the layout of your WordPress website before we start teaching you how and why hackers hack pages. It consists of files and a folder. WordPress files often contain all settings and parameters, while all posts, comments, users and a lot of other items are saved in the archive.
To create the frontend of your website, both elements are required. Yet they can also be abused by hackers as well.
Next, let’s have a look at how WordPress sites get hackers inside.
Note: This is not a guide about how to hack a website using WordPress. It’s an educational post to teach you how hackers can target your site’s hacking vulnerabilities. Having said that, let’s begin.
6 Common vulnerabilities that allow hackers to hack sites with WordPress
It ought to have a point of weakness to hack a website. The common vulnerabilities found on WordPress websites are listed here:
1. Running Outdated WordPress Installation
According to a 2018 survey, about 44 percent of compromised WordPress websites operate on obsolete installations. As a website user, you can find regular WordPress installation updates available, such as:

Updates typically have new functionality, bug fixes, or problems of incompatibility fixed. They still bring WordPress protection updates occasionally. This ensures that if the app has a security vulnerability, the developers will patch it easily and release an upgrade that will delete the flaw.
When published, the public is made aware of the existence of a WP security vulnerability. Then hackers look for websites that have not been updated, find the vulnerability and use it to hack the site.
So if you opt not to upgrade the installation of WordPress, then you haven’t installed the latest security updates and have given the hackers your website on a platter.
Always keep your WordPress website updated.
Tip: Fixes on defence are carried out as small changes. If it is V5.2 or V5.3, you can say if it’s a major upgrade. For instance, a minor upgrade will be V5.2.1. By default, it’s automatic for small upgrades, but you can turn it off. For small changes, we suggest having the Auto-Update function turned on.
We firmly recommend that you keep your WordPress salts and security keys updated, in addition to having your extensions, themes, and core updated.
2. Using Weak Credentials
For hackers, another common entry point is poor passwords. Hackers use a technique called brute force attacks, where they programme bots to search them on the internet for WordPress pages and try to hack into the website with multiple variations of usernames and passwords.
They are now one step closer to getting access to your site if you have left your login name as ‘admin’. If you’ve used famous passwords such as ‘password123’, though, then it’s simple for them to guess it. Thousands, if not millions, of hacking attempts can be made by these bots in just a second (recommended reading: WordPress login security guide).
To make your password as secure as ever, we suggest changing the password to a passphrase in conjunction with numbers and symbols:

3. Having Pirated Themes Installed
Premium themes are appealing, and for our website to make it exclusive, we would all love to have a fantastic theme. Website owners also fall victim to free, cracked or pirated copies of those subjects. These themes can bear pre-installed malware from unreliable sources. You’ll even run the ransomware by downloading it on your WordPress website. This gives hackers the door open. Will have detailed how this is going to happen later.
Often import themes from trusted sites such as the WordPress repository or ThemeForest and ThemeTrust marketplaces only.
4. Using Vulnerable plugins
To find loopholes in the security of plugins, hackers are always on the prowl. They’ll search the internet for WordPress pages that have the plugin enabled, if they spot one. In a matter of minutes, this helps them to break into thousands of websites.
Developers can feel that they can’t manage it anymore and abandon the plugin several times, particularly with free plugins. The protection of the plugin will lapse in these instances and getting it mounted on your site poses a threat. Install plugins only from reputable sites, such as CodeCanyon or the WordPress repository.
Remove WordPress plugins and templates frequently that you don’t need any more. To see how they are being modified and supported by the manufacturer, review the status of the plugins you use.
5. Use Local System Vulnerable Often
It could be your own machine that isn’t secure, they can quickly enter the WordPress site if anyone breaks into your system, since the wp-admin is still logged in and available in most situations. If you do not have a firewall or anti-malware tool installed on your device, this can happen.
It is advised that you never use a public computer on your local infrastructure or a public unsecured wifi network that you use to run your WordPress website.
Still keep the site’s malware identification tools working.
6. Using Bad Support for Web Hosting
We prefer to search for the cheapest one when picking a hosting plan.
But effective security controls don’t necessarily promise the cheapest ones. Shared servers may be cheaper, but they put the website at risk as well.
You can’t say which places you share a web server with and what security policies have been enforced. There are chances that if they get hacked, the malware infection will also spread to your website. There are also occasions that website administrators are hacked, which suggests that hackers are vulnerable to the manipulation of all websites on the hosting network.
Catch up on what they do and what consumers had to say about them when picking a web host.
This will assist you in getting a clear idea of which web host to use. Hackers build their own bots or use free vulnerability scanners available online to search through the internet to locate a compromised site.
When they discover it they can take advantage of the security bug it has (like the ones listed above to enter the WordPress website files or folder. Then, they insert malware that conducts malicious operations such as delivering spam emails, marketing illicit goods, etc.
They also insert code to build new user accounts or backdoors for WordPress that will support them if they try to restore access to your site.
How to Hack a Website on WordPress?
There are endless ways of breaking into a WordPress account. Here to build a new user login, we will address two of the most common ways hackers insert code into your website:
Through Files (Pre-Installed Malware in a Pirated Theme)
Many WordPress domain owners fell victim to pirated themes, as we discussed earlier. For cheap, you get all the features! But to build a new login ID, such applications can include a script. The new user account is created after you update the theme, and the hacker will easily log into your WordPress admin website.
We are going to teach you how you can use your theme file to build a new user account on your WordPress website. This will allow you to understand how pirated themes help your site to be hacked by a hacker.
Tip: If you’re locked out of your wp-admin but still have access to your web hosting account, this can also come in handy.
Caution:
It’s a dangerous affair to go behind the scenes of a WordPress blog. On a research or staging spot, it’s best to do this. Please ensure that you make a secure backup if you want to do so on your live website. You will recover your WordPress backup in case anything goes wrong.
Step 1: Login to your WordPress hosting account. Access the File Manager and go to cPanel.

Step 2: Your WordPress files usually reside in a folder called public_html. Inside it, you can access wp_content/themes.

Step 3: Here, you need to choose the active theme on your website and edit the functions.php.

Step 4: Copy and paste the following code at the end of the file. (If there is a closing tag like so ?>, make sure the code comes on the line before this.)
[php]$new_user_email = ’email@example.com’;
$new_user_password = ‘password’;
if(!username_exists($new_user_email)) {
$user_id = wp_create_user($new_user_email, $new_user_password, $new_user_email);
wp_update_user(array(‘ID’ => $user_id, ‘nickname’ => $new_user_email));
$user = new WP_User($user_id);
$user->set_role(‘administrator’);
}
[/php]Edit the first two lines of your chosen email and password. The code will be executed until you save the file and open your website and you will log in with these new credentials.
We hope you realise now that a new user account will be created when you load a pirated theme if it has this block of code. All the hacker needs to do is enter and log into the credentials.
Through Database – SQL Injection
This is another one of the most common reasons that hacking is performed on WordPress pages. You need to know two things about SQL injections in order to start:
- As the default database system, WordPress uses MySQL.
- WordPress uses SQL queries to retrieve data from the servers in order to create the frontend of a website.
For now, we do not need to talk about what this is or the specifics of it. What you need to note is that you only have access to this database through cPanel > phpMyAdmin. Yet hackers, without using cPanel, find ways to reach it. One of the most common ways in which hackers contact the database of a site is through insecure website formats.
A form is any feature that can be typed into text, such as the WordPress login bar, contact form, comments on the WordPress blog, subscription pop-ups, checkout pages, and the search bar for the site.
The hacker will insert their malicious SQL commands rather than entering the information demanded in the form. This malicious code will make its way in when all data entered into the form gets stored in the database.
To explain how this works, we are going to teach you how to use your database to build a new user account.
Creating New User Account Through Database
Step 1: Access cPanel and open phpMyAdmin > Databases.

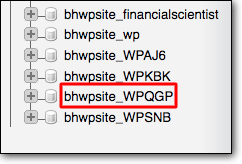
Step 2: Here, you’ll see a list of databases. You need to select your database. (If you don’t know your database name, you can find out this information in your wp-config, like so).

We’ve selected the database according to the name in the wp-config file.
Step 3: Next, from the tables that populate on the right panel, you need to find the table that ends in _users (It will most likely be named wp_users).

Step 4: Here, you can click on ‘Insert’.

Step 5: It will open up the following screen where you can enter the user login name, password, email and display name.

Step 6: Next, click on ‘Go and your changes will be saved. Now you can use the latest passwords to log into WordPress.
Through injecting a block of SQL code into the database, the same can be achieved. If the code enters the database, it will run and a new user will be created, similar to the pirated theme. We can think of it as a hacker in your home literally making their own door and walking on in.
How To Stop Hackers From Hacking Your Website?
In order to make your site safe enough to keep hackers at bay, there are four key steps you need to take:
Install a WordPress Security Plugin
A protection plugin like MalCare is required on any WordPress website. With such a plugin that will search the website daily, secure your WordPress account. It can track any unusual actions, interrupt malicious traffic and keep hackers out. You will be warned automatically in case a hacker breaks in and you will clean your website quickly before they can do any harm.
Install an SSL certificate
This certificate would have data encryption for your website. What this suggests is that data is passed between their machine and the server of your website anytime someone visits your website.
If it is conveyed in plain text, the information can often be intercepted by hackers lurking around. It can be read, stolen or changed to their taste by them.
But if its encrypted, even if a hacker gets a hold of it, they won’t be able to decipher it.
You can get an SSL certificate from your web host or from an SSL provider. If you’re worried about spending too much on a certificate, providers like LetsEncrypt offer free SSL.
To learn how to instal an SSL certificate, take a look at this guide – Moving HTTP to HTTPS.
Fix Known Vulnerabilities
As we mentioned earlier, there are common vulnerabilities in WordPress. We recommend that you take the following measures to minimise vulnerabilities.
- Updating WordPress and its themes and plugins must be top priority.
- Ensure you always use strong login credentials to avoid brute forcing attacks.
- Regularly delete unused themes and plugins
- Never ever use pirated themes and plugins. Always download such software from trusted sources like the WordPress repository, CodeCanyon or ThemeForest.
- Use a reliable web hosting service provider.
- Keep your local computer protected by installing anti-malware software.
Harden Your WordPress Site
WordPress recommends that every website on their platform takes certain steps to harden their sites. Some of these measures include:
- Keep an active WordPress firewall. This will help block Limiting the number of login attempts. Every user gets only three chances to enter the credentials correctly, after which they will have to opt for ‘Forgot password’ or contact the admin. You can use the same MalCare plugin to implement this step.
- Disabling plugin installations in case you have multiple users working on the website. You would want to ensure no one instals a plugin freely without checking if they are reliable and trustworthy to have your site. This can be done manually by editing a file called wp-config.php in your WordPress install. You can also use the MalCare plugin for this.

To verify the person logging in, implementation of 2-factor authentication. This is achieved by sending the registered mobile or email a one-time password, or by using apps such as Google Authenticator that generate a password every 30 seconds in real time.
There are many more ways in which your website can harden. These steps are recommended to be implemented as per the requirements of your website.
Ultimate Thoughts
We hope that this report has provided you a clearer understanding of how your website can present bugs and how hackers get in. Hackers are not racist and just about every site will be hacked. There is a very high risk that you would be compromised if your site is insecure.
To sum up, we suggest mitigating bugs, adding a protection plugin, and hardening the website so that your website is not likely to be accessed by hackers.















Leave a Reply